Search for a specific file type and then list them in the custom inventory field
Hi all,
Is it possible to create a custom inventory rule which searches for specific file types in the last logged on user folder (windows 7) then display the results in the computer inventory under custom inventory fields?
Thanks
Answers (4)
Not sure how you would go about enumerating them into inventory, or knowing the LAST logged on user, but it is possible to list items for current user and return them attached TO the inventory in a way....
First create a batch file that runs a command like this.
dir %USERPROFILE%\Downloads\*.exe /s>C:\Programdata\Dell\DownloadItems.txt
When you run the batch it would create a txt file in the Dell directory with a list of the exe's in the logged on users downloads.
Then in an Online KSCRIPT you choose the action of Upload file
Choose path of C:\Programdata\Dell
Choose FIle DownloadItems.txt
After running it on the computer inventory you should see a new item under software /uploaded files and it will be the DownloadItems.txt file with the list of executables.
It may be able to be modded to fit your needs.
I will blog a working example tomorrow when I have a little more time and place a link in this thread.
This kind of task is better handled with a script, like jdornan is recommending. You can have the script upload the file, or you could have a script that outputs to a file and have a custom inventory rule read the contents of the file.
If you want to run reports on this item then I believe you need to use a custom inventory rule.
Also, custom inventory rules are system wide, so if you want to target only certain machines to collect this data from, then scripting is the better way to go.
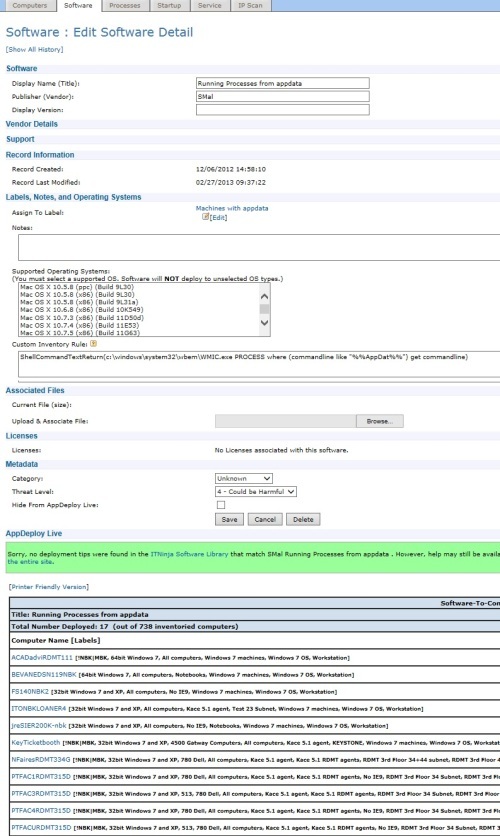
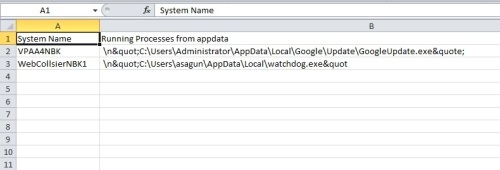
I have a software item simular to what you want. You would have to figure out how to plug the last user in as a varible or even use lastaccessed timestamp in your query.
I have one item that looks for running process's in the users appdata area to watch for malware.
ShellCommandTextReturn(c:\windows\system32\wbem\WMIC.exe PROCESS where (commandline like "%%AppDat%%") get commandline)
You should be able to use this one to look for exe's and add the timestamp when you figure out the format. it would be "and lastaccessed like 'timestamp'"
The timestamp will have the format YYYYMMDDhhmmssddddddZZZZ where
- YYYY = year
- MM = month
- DD = day
- hh = hour (24 hour format)
- mm = minutes
- ss = seconds
- dddddd = micro seconds
- ZZZZ = timezone, expressed as minutes difference from GMT (the 1st character is the sign)
ShellCommandTextReturn(c:\windows\system32\wbem\WMIC.exe datafile WHERE "drive='c:' AND path like '\\users\\%%' AND Extension='exe'" get name)
Comments:
-
you can also OR this for multiple extensions.
WMIC datafile WHERE "drive='c:' and path like '\\users\\%%' AND Extension='mpg' OR drive='c:' and path like '\\users\\%%' AND Extension='jpg'" get name - SMal.tmcc 11 years ago -
I was afraid to edit the above answer, that could corrupt the symbols. So see other answer for pictures of item and sample output report from the label. - SMal.tmcc 11 years ago