K2000 PXE Security Issues
We are new to the K2000 and still in the setup and testing phases. One question I have which I haven't seen referenced elsewhere regards security practices around PXE booting machines. We will have the K2000 setup so that we can reimage labs in place but I'm concerned with what happens if a student tries PXE booting a machine on their own. With the default configuration when a machine boots to the KBE it offers you the option to re-image the machine without prompting for any sort of password. Is there any way around that? It seems like there should be a way to stop users from imaging systems on their own but I haven't seen that in the documentation.
Thanks.
0 Comments
[ + ] Show comments
Answers (1)
Answer Summary:
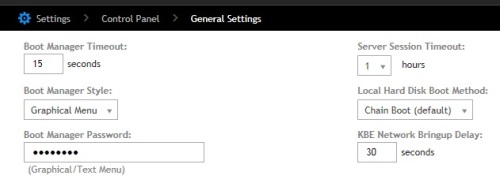
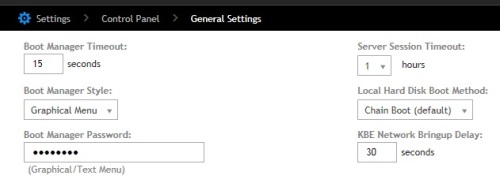
The interface was showing that a password was set but until I changed it I was not being prompted for a password. Once I made sure a password was set I was prompted at the PXE menu.
The interface was showing that a password was set but until I changed it I was not being prompted for a password. Once I made sure a password was set I was prompted at the PXE menu.
Please log in to answer
Posted by:
SMal.tmcc
9 years ago
set the password for the pxemenu on the general settings page.
Comments:
-
I have a password set there but I am not prompted for it when the machine boots. - chucksteel 9 years ago
-
you will prompted, if you choose a KBE to be booted, not in the PXE menu - Nico_K 9 years ago
-
I reset the password and I'm being prompted now. I'm pretty sure a password was set previously and it showed black dots like there was a password there, but until I changed it I was not prompted.
Thanks. - chucksteel 9 years ago-
The UI will show black dots even for a blank password. - andrew_lubchansky 9 years ago