What does "Not Patched" mean?
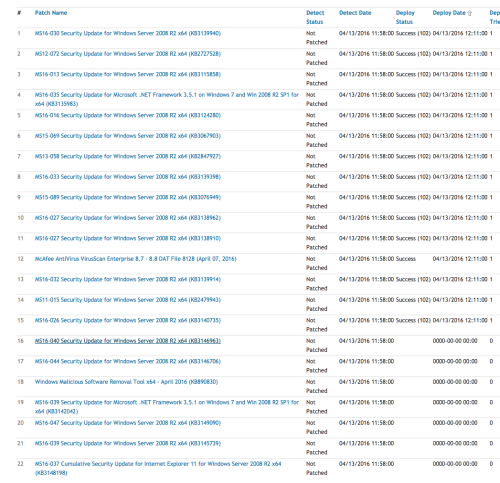
Just curious why it always says "Not patched" if I run only a detect, then it returns patches that are needed with the detect status as "Not Patched", but if I run a detect and deploy, it still says Not Patched even for those patches that deployed.
Thanks!
1 Comment
[ + ] Show comment
-
Did the system reboot after the patch update? If not, then the system will need a reboot before the detect status changes from Not Patched. Once the system reboots, the system will be scanned again and should update the status. - KACE_Irwin 8 years ago
Answers (2)
Please log in to answer
Posted by:
FrankVillanveva
3 years ago
Patch and all meaning are full of the shows for the individuals. The size of the patch and master papers is issued for the management of the field. The structure is vital for the program and all changes for the citizens in this ambit and scores for all ideal paths for humans.
Posted by:
StockTrader
8 years ago
Hello,
NOT PATCHED simply means that the 'vulnerability' has not been patched yet.
Should it be patched? Should someone install a fix for this? there are not standard answers: it depends by your needs.
The detect and deploy job configuration has two sections: what you like to detect (all the patches or some of them specified by one or more labels) and what you like to deploy (all the patches or some of them specified by one or more labels) and it's not required that the two sections need to be symmetrical.
You may decide to Detect for all the patches and deploy only the OS critical ones for example.
There is even another problem: let's say that you have a deploy and detect job that detects all the patches and installs all of them: you need to consider that not all the remediation content is immediately available on the K1000 (and/or eventually configured replication shares).
In a standard configuration the K1000 downloads every night only the signature of the patches and every 30 minutes the remediation content for the patches detect by detection jobs.
So it may happen that you detect on a device the need for 140 patches but in the database you have only the remediation content for 40 of them.
What happens to the other 100? They're not installed because the remediation content is momentarily missing, they are added to a ''patch content wish list'' that is processed every 30 minutes.
I hope this sheds a bit of light on the process ;-)
Kind regards,
Marco - StockTrader



