Inspired by mpace's post I figured I would chime in and give an alternate path for creating a bootable linux distribution that will also work with microSD's. This one will have an added bonus of installing and using the LUKS encrypted volume's very fun Nuke option.
Note: if you already have a bootable distro and want to skip to the LUKS NUKE portion of the article towards the bottom.
mpace's article:
http://www.itninja.com/blog/view/create-a-bootable-encrypted-usb-running-linux-mint-16
What you will need:
- Ubuntu, Kali, or Mint iso
- USB drive or microSD and USB adapter
- Rufus
- Cheetos
As mpace mentions in his article, fast media is paramount. A slow thumb drive is still usable but we're all used to instant gratification so spend the bucks on a nice 3.0 I too enjoy the company of a SanDisk Extreme 3.0 - they're fast, they're sleek, they're tacticool black, and the clicking soothes me for some reason. Lately PNY has had their Turbo line of 3.0 drives on sale and have caught my eye; like this
128gb for $47 at time of writing.
You may also use microSD's with this path. I try to stick with fast drives here as well; looking for class 10 or UHS1 whenever possible. Lately I've been going with the
Samsung Pro line since they're a good price and 90MB/s. Most microSD's aren't as fast as the USB counterparts (most clock in at 30MB/s some as high as 90MB/s) but, if you want the convenience of multiboot without the hassle of swapping drives or re-partitioning your whole computer - rock a microSD. For this option you will need a USB to microSD adapter for the purposes of burning the image. (I'm partial to this
IOGear) If you plan on leaving this in a laptop that has a half height SD slot *cough*Macbook*cough* there are plenty of flush-mount options out there
like this one or use your imagination/Google-fu to find one to suit your needs.
Now that you have all your hardware handy and you've downloaded
Rufus we can start the process. Time to go
download an Ubuntu iso.
The torrent option is often much quicker but torrents are bad and should be avoided at all costs, right? You can use Kali if you'd like, or Mint, or another distro but today we'll focus on Ubuntu to make life easier.
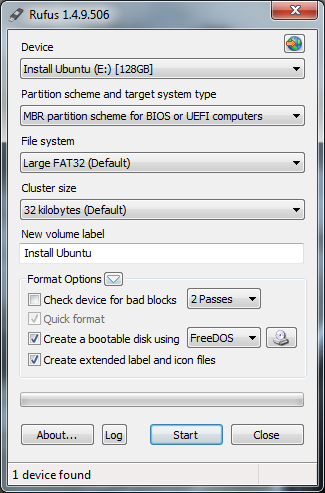
1. Plug in your drive and execute Rufus
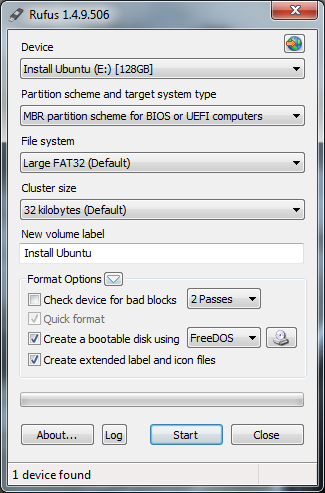
2. Verify the Device that shows up in the drop down is, in fact, the device you want to permanently format and overwrite data. If you're using a microSD it has to be in a USB to microSD adapter to show up for Rufus.
3. Pick a Partition Scheme to use. Most systems will accept BIOS or UEFI but I have found that some devices like the Surface Pro prefer MBR for UEFI only
4. Click the drop down for FreeDOS and change it to ISO Image, click the icon next to it, and select your ISO
I usually leave the rest as default and rename it to something more fun than the name of the ISO. Be creative the NSA is watching.
5. Once you click start it will give you one finally warning stating everything on said drive will go bye bye. Click ok and the process begins (sometimes this can take a couple minutes)
6. Once completed close everything, plug the USB or microSD into the target machine, reboot, and verify everything boots fine. Most distro's will ask if you want to install at this point. Go ahead and install using the encrypted option (usually listed as LUKS or LVM) but make sure you're installing on the USB/microSD not your primary hard-drive.
Installation of the OS is straight forward - pick your timezone, setup passwords, eat some cheetos, pick a keyboard layout, enjoy.
7. Reboot back into the newly created bootable USB/microSD linux distro and enjoy. To protect your data that much more....see below
LUKS NUKE TIME!
Well fancy seeing you here.
Encryption is fun and these days almost required to keep our data safe. This Nuke feature allows you to have two entirely different passwords for the OS boot process: One password lets you in as normal and another one destroys the encryption keys rendering your data useless. In the case of Kali linux you need to be on 1.0.7 or higher for this to work (the nuke option is actually already installed so you don't have to go through the patching process...skip to the last command) I'm not sure what versions are required for other flavors of linux - google may know. Today we're going to look at it on Ubuntu 14
Boot up your distro and log in then find terminal. (I used a VM for testing purposes to see the Nuke feature in action without hosing my EDC drive) Execute the following commands and please note that sudo will require authentication/if you are root you can ignore sudo.
sudo apt-get install libgcrypt11-dev libdevmapper-dev libpopt-dev uuid-dev libtool automake autopoint debhelper xsltproc docbook-xsl dpkg-dev
sudo apt-get source cryptsetup
There should be a directory created for cryptsetup-1.x.x you'll need that info later
sudo apt-get git
I had to run this for Ubuntu 14
sudo git clone https://github.com/offensive-security/cryptsetup-nuke-keys
cd /cryptsetup-1.x.x
Told you you'd need it later
sudo patch -p1 < ../cryptsetup-nuke-keys/cryptsetup_1.4.3+nuke_keys.diff
sudo dpkg-buildpackage -b -uc
sudo dpkg -i ../libcryptsetup*.deb
sudo dpkg -i ../cryptsetup*.deb
cryptsetup now has
AddNuke feature
sudo cryptsetup luksAddNuke /dev/sdaX
If you're using Mint/Ubuntu it's usually sda5
but verify
It will ask
for your current passphrase, enter it, and you'll then be prompted for a new
passphrase for keyslot (this is the nuke password)
When you boot linux you will be prompted for a password. Enter the correct password and it let's you boot as normal and you can access all your data as normal. Enter the nuke password and it simply says "bad password" There will be no "destroying data please wait" flashing across the screen. Entering the nuke password kills all the encryption keys rendering data the useless.
Bootable Linux Distro - Check
Full Disk Encryption - Check
Killswitch - Check
Happy Hunting =^..^=


Comments