Using the K1000 to disable or even remove a service on clients
Our enterprise deployed Microsoft's UPHClean (User Profile Hive Cleanup) utility prior to a domain migration on all our Windows XP/Server 2003 hosts. In most instances, this application, even though it was deployed using msiexec, does not show up in Add/Remove Programs but is still active as a system service.
I would like to clean this service off of all our hosts as it serves no purpose and is causing some small havoc on certain hosts as it's still looking for the old domain. However, it does not show up in K1000 inventories of installed software on the affected hosts. Is there a way I can use the K1000 to remove or at the very least disable this service on every host in our domain where it still resides?
My research so far has not been successful.
Answers (4)
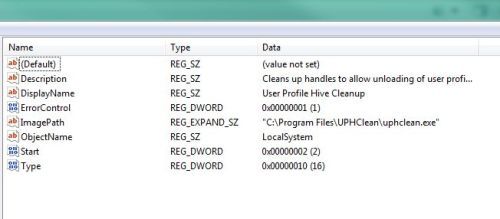
From tshupp: 1) Create a Custom Inventory rule using the following syntax: RegistryKeyExists (HKLM\System\CurrentControlSet\Services\UPHClean) 2) Create a new Machine Smart Label in K1000 to find KACE clients that match the Custom Inventory Rule. From SMal.tmcc: 3) Under K1000 Scripting choose the Configuration Policy tab and then select "Enforce Registry Settings" to create your script that you'll apply against the Smart Label clients. 4) Syntax for the script in this particular case (disabling the service) should be: [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\UPHClean] "Start"=dword:00000004 5) Make sure to include the line break after the registry location. Save the script and apply it after testing.
I believe it creates a registry key and subkeys at:
HKLM\System\CurrentControlSet\Services\UPHClean
You could create a custom inventory rule to identify machines with that key. That would ID the systems with it installed. Then use managed installs to remove via command line. There are a few uninstall strings found here, under inventory records:
http://www.itninja.com/software/microsoft/user-profile-hive-cleanup-service/1-15044
I'd take a look again for a software entry, though... as those inventory records are reported by customers' K1000s.
Comments:
-
Thanks for the info. I'll have to look into how to craft the custom rule and see if I can find something similar. I'm SQL-ignorant. - KFox 11 years ago
-
Custom registry rule for a registry key should be:
RegistryKeyExists (HKLM\System\CurrentControlSet\Services\UPHClean)
Give the software entry a name. (I like to preface all of my custom inventory rules with 'CIR:' so they stand out) You can then create a simple smart label (as SMal suggested) searching for software which matches 'CIR: UPHClean' or whatever you name it. Once you have the smart label, you can target either a script or a managed install. Managed installs can be used to uninstall, so if you're unfamiliar with scripts, that might be a different route to take. - tshupp 11 years ago
-
Thanks, tshupp. I've created the Custom Inventory rule based on what you wrote above and it's polling successfully. - KFox 11 years ago
You can run a script based on the lable tshupp mentioned also. You can create one manually or use the configuration policy -enforce registry settings to create a quick script. Also you may just want to disable that service vs deleting the key. To disable change the "start" key to 4.
Comments:
-
Steve,
Thanks for the suggestion. Unfortunately, I don't know how to create scripts yet. The couple that I've implemented were ones I found. I'll look into it some more. I see the configuration policy. Now I'll just have to research the syntax. - KFox 11 years ago -
to delete the key
reg.exe /delete HKLM\System\CurrentControlSet\Services\UPHClean /f
to disable
reg.exe /add HKLM\System\CurrentControlSet\Services\UPHClean /v start /t REG_DWORD /d 4 /f - SMal.tmcc 11 years ago-
Steve,
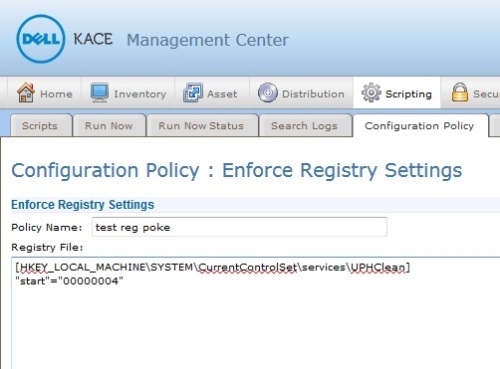
Thanks again for your continued help. I did create a script with the configuration policy > enforce registry settings tool, and I copied your syntax above for disabling the service. I then ran the script against one test machine, but it didn't change the "Start" value to 4. It remained at 2. Not sure where the problem lies, but I'm guessing it's what i actually put in the script.
I'll poke at it some more. - KFox 11 years ago-
see pic I posted as new answer for syntax. - SMal.tmcc 11 years ago
Comments:
-
Steve,
I altered the script I have to match your syntax, but I'm still not having any success. Registry key on my test system is still showing a value of "0x00000002(2)."
I've added pics of my configuration and the results on the test PC after running the script. - KFox 11 years ago -
Thanks, Steve! That did the trick. Now I can apply it to my machine smart label. - KFox 11 years ago
Comments:
-
try putting it on two lines like I did, all of our working registry policies have two lines.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\UPHClean]
"start"="00000004" - SMal.tmcc 11 years ago-
I am not sure what kace does in the background to run this but if they do it as a merge file this matches a typical merge file layout
example of reg merge file:
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\UPHClean]
"Type"=dword:00000010
"Start"=dword:00000004
"ErrorControl"=dword:00000000 - SMal.tmcc 11 years ago -
I can do run now in the script with this layout and refresh the registry editor and see the change. - SMal.tmcc 11 years ago
-
That's what I saw as well. I ran the script against a remote PC on which I had a network registry view, and after the successful run of your script, I refreshed and saw the change. - KFox 11 years ago
-
I commented in the wrong spot above, so here's another:
That splitting of lines did the trick, Steve. Thanks for all your help and patience with my n00bery. - KFox 11 years ago
-
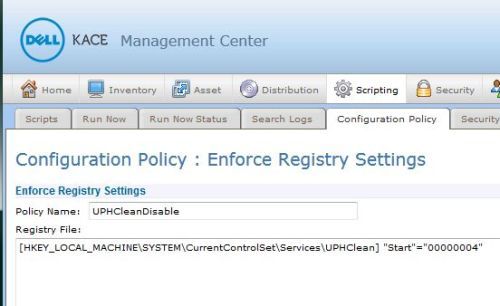
Actually, it wasn't quite resolved yet.
Instead of creating a DWORD value of 0x00000004(4), the script created a REG_SZ value of 00000004. I looked at your comment above detailing an example of a reg merge file and changed the second line to say "Start"=dword:00000004 and then tested successfully against several hosts.
Thanks again. - KFox 11 years ago