How to add the contents of a file to the Custom Inventory Field.
I need to find all of the laptops in our organization that have an incorrect setting that is controlled by a text entry in a .def file. I have a .def file located on the HDD at C:\Program Files\Anzio15\RISC1 (VPN).def and I need to get KACE K1000 to read its text and paste the contents under the Custom Inventory Fields of the Device's Inventory. This way I can create a smart filter that will find all of the devices that have "commtype=2" in that file...
I have tried: going to Inventory>Software>Choose Action>New. Named the new software record, publisher, and version (just make up anything as long as it makes sense to me right?). About midways down in "Custom Inventory Rule" nothing I have tried works, I entered;
1. ShellCommandTextReturn(cmd.exe /c type C:\Progra~1\Anzio15\RISC1(~1.def)
2. ShellCommandTextReturn(cmd.exe /c type "C:\Progra~1\Anzio15\RISC1(~1.def")
3. ShellCommandTextReturn(cmd.exe /c type "C:\Progra~1\Anzio15\RISC1(~1.def\")
4. ShellCommandTextReturn(cmd.exe /c type C:\Program Files\Anzio15\RISC1 (VPN).def)
5. ShellCommandTextReturn(cmd.exe /c type "C:Program FIles\Anzio15\RISC1 (VPN).def")
6. ShellCommandTextReturn(cmd.exe /c type "C:Program FIles\Anzio15\RISC1 (VPN).def\")
7. ShellCommandTextReturn(cmd /c type C:Program FIles\Anzio15\RISC1 (VPN).def)
8. ShellCommandTextReturn(cmd /c type "C:Program FIles\Anzio15\RISC1 (VPN).def")
9. ShellCommandTextReturn(cmd /c type "C:Program FIles\Anzio15\RISC1 (VPN).def\")
And probably a few others. Every time I save this software inventory and force the inventory on the laptop next to me, it doesn't add anything to the Devices Inventory under Custom Inventory Rule... If, on the laptop, I open a CMD prompt and enter;
1. cmd /c type "C:Program FIles\Anzio15\RISC1 (VPN).def
2. cmd /c type "C:\Progra~1\Anzio15\RISC1(~1.def)"
3. cmd.exe /c "C:\Progra~1\Anzio15\RISC1(~1.def)"
All print the file onto the screen correctly.
So what/where is my error here?
Thanks,
1 Comment
[ + ] Show comment
Answers (1)
Please log in to answer
Posted by:
admama
7 years ago
I was trying to do exactly the same thing and I have found my mistake.
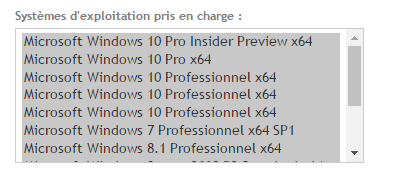
I did not have select the operating systems when I have created the custom inventory field.
Comments:
-
That is not my problem, I have all the OS's highlighted blue. It still won't work. Do I need to tag systems to make the software inventory check the computers somehow or is this done automatically when the computers do the inventory check in? - jrenaud 7 years ago
-
the CIR will be run if a check is running.
In my case I use a similar one:
ShellCommandTextReturn(cmd /c more c:\programdata\dell\kace\amp.conf|findstr disableloginsplash) (works not with 6.4 since the string is not in the amp.conf of a 6.4 agent but in the amp_auto.conf, but before and also in 7 it is)
Highlight all OS, set the CIR like that and force a check in.
If it still don't work:
enable debug on the agent and run the check in. Check the logs of the agent for error messages. If unsure, post them here or contact support. - Nico_K 7 years ago-
I tried ShellCommandTextReturn(cmd /c more c:\progra~1\Anzio15\RISC1(~1.def| findstr commtype=) with no luck.
If I open a cmd prompt and put in "cmd /c more c:\progra~1\Anzio15\RISC1(~1.def| findstr commtype" it returns commtype=X.
Which logs should I post? Should I post the contents or upload the log somehow? - jrenaud 7 years ago


ShellCommandTextReturn(cmd.exe /c type "C:\Program Files\Anzio15\RISC1 \(VPN\).def")
or
ShellCommandTextReturn(cmd.exe /c type "C:\Progra~1\Anzio15\RISC1\(~1") - flip1001 7 years ago