Hello from TechEd 2013! I had the pleasure of attending a session with renowned professional penetration testers, diving into security changes as well as current challenges that are present in a Windows 8 and Server 2012 infrastructure. Among some of the information relevant to the systems administrator's day-to-day operations:
Debugging Mode
When booted into debugging mode, past iterations of Windows would alert the user that they were in fact in debugging mode and a remote system may or may not be connected and "debugging" their computer. This alert was present in the form of rectangular notifications in each corner of the client screen. In Windows 8, this behavior has changed. Here is a screenshot of Win8 running in normal, non-debug mode:
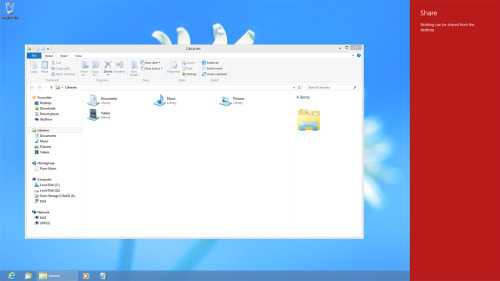
And now here is a screenshot of Win8 running in debugging mode with another computer connected and with full control:

Did you catch the difference? The debugging mode notifications have been removed in Windows 8. You can still see if debugging mode is enabled by running bcdedit from a command prompt and looking for the debug property configured as enabled.
Configure IPv6
Are you running IPv6? Do you have it configured properly? If the answer to either of those questions is "I don't know" it's worth finding out. IPv6 can be remotely configured and Windows will always choose an IPv6 connection over an IPv4. This can potentially open up your environment to man-in-the-middle style attacks if IPv6 hasn't been configured.
Disabled "guest" Account Still Allows RDP Access
By default, the Guest account is set to disabled and does not allow the account to login to a system. However, when attempting a Remote Desktop session, using DOMAIN\guest and a blank password will pass the RDP traffic and establish a connection. A hard stop occurs at the Windows login, notifying you that the account has been disabled and to contact your system administrator. The problem is that the RDP session has already been established and data is flowing! Thankfully, this has been addressed in Windows 8 and Server 2012 and the disabled Guest account no longer presents this vulnerability.
Ping -t
Not really critical but intersting nonetheless. Running ping.exe with -t switch, according to the documentation, is supposed to run the ping command indefinitely. The code actually specifies the command to run for 99 years. If you're luckily enough to kick off a ping.exe -t and see it actually finish then you are quite lucky indeed. 

Comments